OpenSSL 1.1.1l (64-bit)
- 2024 軟體跟著走
- 影片播放
- SplitmediaLabs, Ltd.
- 未分類
- 評價 0 分
- 此版本檔案下載
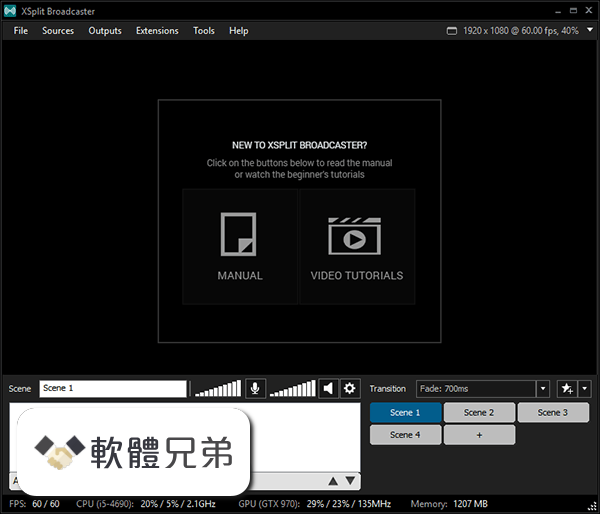
它比以往更容易添加,調整大小並重新定位您的攝像頭,無論是流媒體還是錄製遊戲。激活色度鍵,使您的廣播更加身臨其境使用綠色屏幕透明效果.
如果 XSplit Broadcaster,是你的畫布,那麼多媒體源是你的油漆。製作廣播時,將視頻和音樂中的所有內容添加到網絡攝像機和 Skype 中的遠程訪客。利用增強的音頻功能提供更高保真的聲音,並在使用我們的場景預覽編輯器前預覽和編輯新的鏡頭.
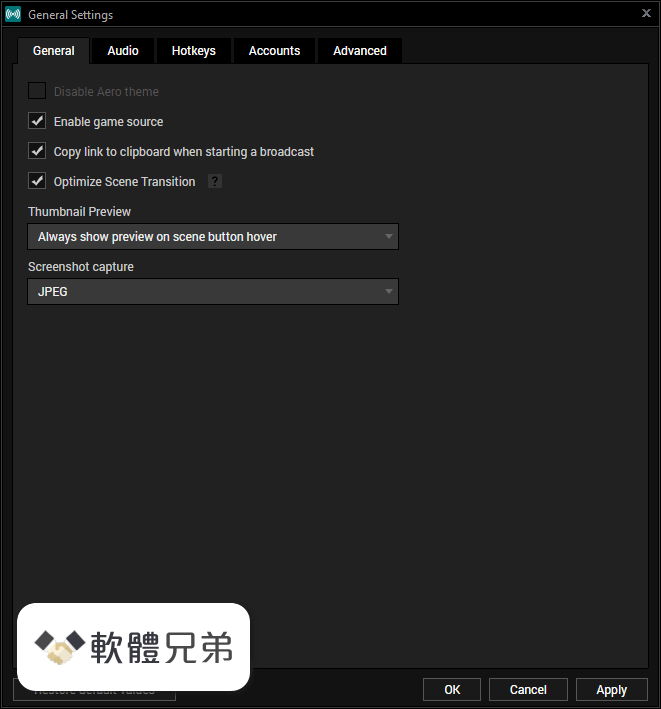
XSplit Broadcaster 由於我們的插件存儲,具有豐富的自定義功能,讓您進一步個性化您的廣播捐贈警報,音樂請求和更多。你甚至可以開發自己的!可能性是無止境的.
注意:演示版本中有限的功能.
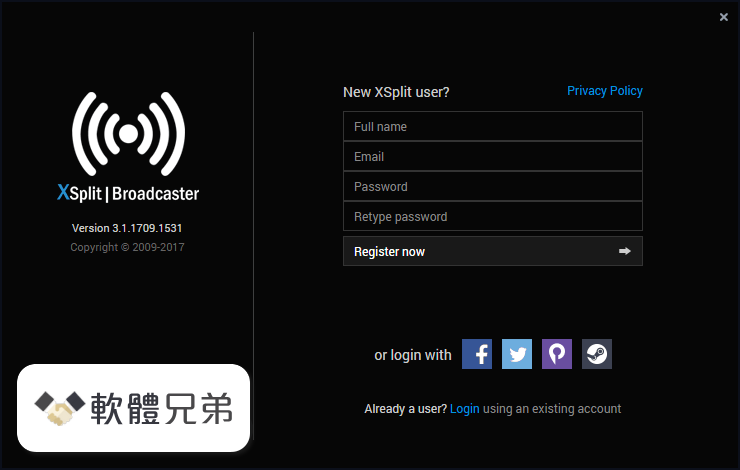
ScreenShot


| 軟體資訊 | |
|---|---|
| 檔案版本 | OpenSSL 1.1.1l (64-bit) |
| 檔案名稱 | Win64OpenSSL-1_1_1L.exe |
| 檔案大小 | |
| 系統 | Windows 7 / Windows 7 64 / Windows 8 / Windows 8 64 / Windows 10 / Windows 10 64 |
| 軟體類型 | 未分類 |
| 作者 | SplitmediaLabs, Ltd. |
| 官網 | https://www.xsplit.com/#broadcaster |
| 更新日期 | 2021-08-25 |
| 更新日誌 | |
|
What's new in this version: Fixed an SM2 Decryption Buffer Overflow: OpenSSL 1.1.1l (64-bit) 相關參考資料
Changelog - OpenSSL
OpenSSL 1.1.1 — Changes between 1.1.1k and 1.1.1l [24 Aug 2021] ... Have 'config' recognise 64-bit mingw and choose 'mingw64' as the target platform ... https://www.openssl.org Download OpenSSL 1.1.0k (64-bit) Free - FileCombo
Download OpenSSL 1.1.0k (64-bit) for Windows PC from FileCombo. Fast update and Free Download Latest Version 2021 - FileCombo. https://filecombo.com Downloads - OpenSSL
A list of mirror sites can be found here. Note: The latest stable version is the 3.0 series. Also available is the 1.1.1 series which is our Long Term Support ( ... https://www.openssl.org OpenSSL
0 is now available: please download and upgrade! 24-Aug-2021, Security Advisory: two security fixes. 24-Aug-2021, OpenSSL 1.1.1l is now available, ... https://www.openssl.org OpenSSL (64-bit) - FileHorse
2021年8月25日 — Latest Version: OpenSSL 1.1.1l (64-bit) LATEST. Requirements: Windows XP64 / Vista64 / Windows 7 64 / Windows 8 64 / Windows 10 64. https://www.filehorse.com OpenSSL - 維基百科,自由的百科全書
TLS 1.3的開發由Akamai贊助。 主要版本釋出[編輯]. OpenSSL版本歷史 ... https://zh.wikipedia.org OpenSSL 1.1.1 and 3.0 x86x64 Binaries for Microsoft Windows
Microsoft Windows OpenSSL 1.1.1l and 3.0.0. 64-bit (Win64 / x64) and 32-bit (Win32 / x86) Binary Distribution. Digitally signed. Download for Free. https://kb.firedaemon.com OpenSSL 1.1.1 Series Release Notes
Major changes between OpenSSL 1.1.1k and OpenSSL 1.1.1l [24 Aug 2021] ... in the x64_64 Montgomery squaring procedure used in exponentiation with 512-bit ... https://www.openssl.org OpenSSL 1.1.1l (64-bit) - FileHorse
2021年8月25日 — OpenSSL 1.1.1l (64-bit). Date released: 25 Aug 2021 (4 weeks ago). Download · OpenSSL 1.1.1k (64-bit). Date released: 26 Mar 2021 (6 months ... https://www.filehorse.com version 1.1.1k - OpenSSL
Changes between 1.1.1l and 1.1.1m [xx XXX xxxx] *) Changes between 1.1.1k and ... [Richard Levitte] *) Have 'config' recognise 64-bit mingw and choose ... https://www.openssl.org |
|
