OpenSSL 1.1.1l (64-bit)
- 2024 軟體跟著走
- 防火牆與安全
- IPVanish Team
- 未分類
- 評價 50 分
- 此版本檔案下載
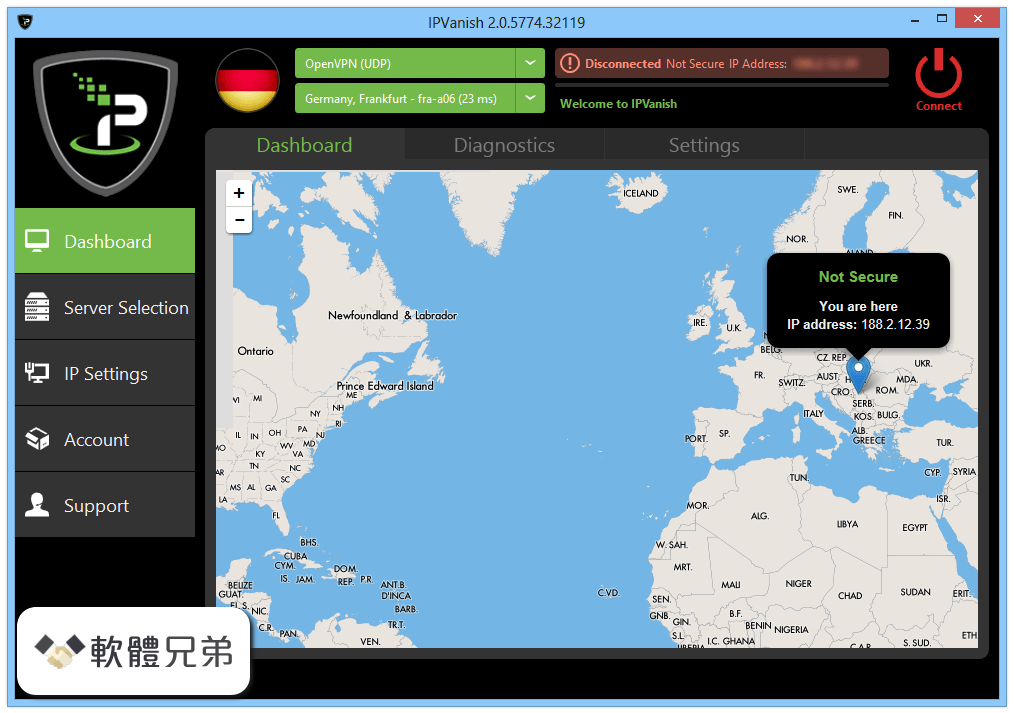
IPVanish 為日常網絡使用提供安全的環境。一旦建立 VPN 連接,所有在線數據(電子郵件,即時消息,數據傳輸,網上銀行)都將通過加密隧道.
IPVanish VPN 特性:
超快速連接
“我們是唯一的頂級 VPN 網絡,意味著更快,更多“
100%在線安全
IPVanish 是保護自己免受網絡威脅和不安全的 Wi-Fi 熱點的最佳方式.
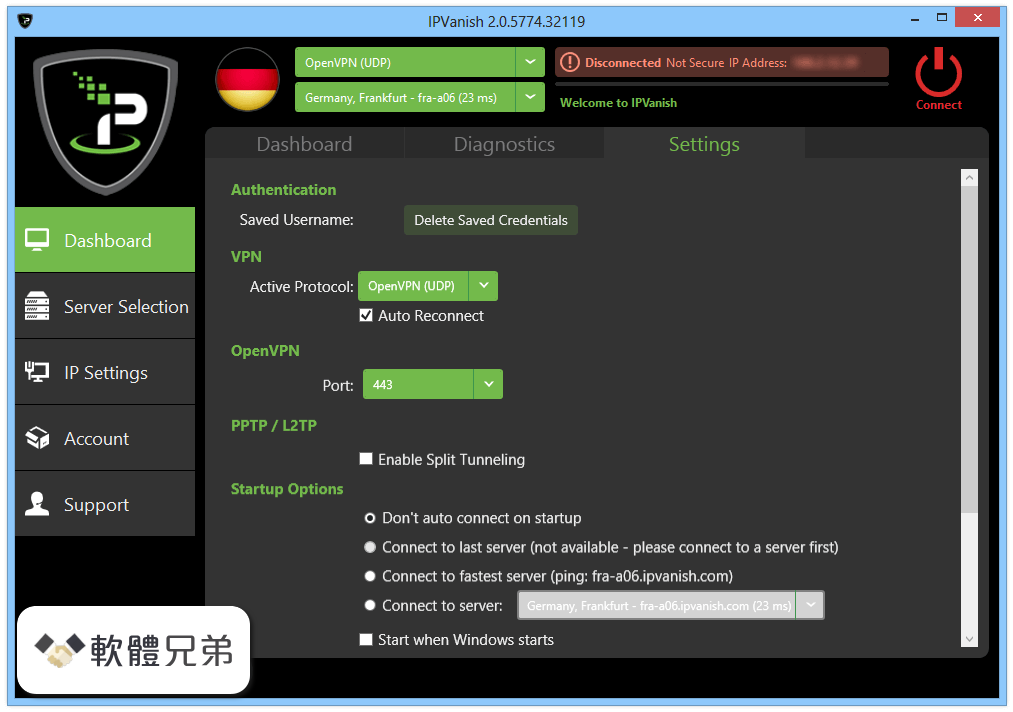
易於使用和免費軟件
簡單的點和點擊軟件為您的所有設備.
最好的 VPN Network
IPVanish 為 60 多個國家的 450 多台服務器提供了 40,000 多個 IP 的安全連接。虛擬地從世界任何地方訪問網頁.
注意:需要.NET Framework。無法在未註冊版本中更改您的 IP .
也可用:下載 IPVanish 為 Mac
ScreenShot



| 軟體資訊 | |
|---|---|
| 檔案版本 | OpenSSL 1.1.1l (64-bit) |
| 檔案名稱 | Win64OpenSSL-1_1_1L.exe |
| 檔案大小 | |
| 系統 | Windows XP / Vista / Windows 7 / Windows 8 / Windows 10 |
| 軟體類型 | 未分類 |
| 作者 | IPVanish Team |
| 官網 | https://www.ipvanish.com/ |
| 更新日期 | 2021-08-25 |
| 更新日誌 | |
|
What's new in this version: Fixed an SM2 Decryption Buffer Overflow: OpenSSL 1.1.1l (64-bit) 相關參考資料
Changelog - OpenSSL
OpenSSL 1.1.1 — Changes between 1.1.1k and 1.1.1l [24 Aug 2021] ... Have 'config' recognise 64-bit mingw and choose 'mingw64' as the target platform ... https://www.openssl.org Download OpenSSL 1.1.0k (64-bit) Free - FileCombo
Download OpenSSL 1.1.0k (64-bit) for Windows PC from FileCombo. Fast update and Free Download Latest Version 2021 - FileCombo. https://filecombo.com Downloads - OpenSSL
A list of mirror sites can be found here. Note: The latest stable version is the 3.0 series. Also available is the 1.1.1 series which is our Long Term Support ( ... https://www.openssl.org OpenSSL
0 is now available: please download and upgrade! 24-Aug-2021, Security Advisory: two security fixes. 24-Aug-2021, OpenSSL 1.1.1l is now available, ... https://www.openssl.org OpenSSL (64-bit) - FileHorse
2021年8月25日 — Latest Version: OpenSSL 1.1.1l (64-bit) LATEST. Requirements: Windows XP64 / Vista64 / Windows 7 64 / Windows 8 64 / Windows 10 64. https://www.filehorse.com OpenSSL - 維基百科,自由的百科全書
TLS 1.3的開發由Akamai贊助。 主要版本釋出[編輯]. OpenSSL版本歷史 ... https://zh.wikipedia.org OpenSSL 1.1.1 and 3.0 x86x64 Binaries for Microsoft Windows
Microsoft Windows OpenSSL 1.1.1l and 3.0.0. 64-bit (Win64 / x64) and 32-bit (Win32 / x86) Binary Distribution. Digitally signed. Download for Free. https://kb.firedaemon.com OpenSSL 1.1.1 Series Release Notes
Major changes between OpenSSL 1.1.1k and OpenSSL 1.1.1l [24 Aug 2021] ... in the x64_64 Montgomery squaring procedure used in exponentiation with 512-bit ... https://www.openssl.org OpenSSL 1.1.1l (64-bit) - FileHorse
2021年8月25日 — OpenSSL 1.1.1l (64-bit). Date released: 25 Aug 2021 (4 weeks ago). Download · OpenSSL 1.1.1k (64-bit). Date released: 26 Mar 2021 (6 months ... https://www.filehorse.com version 1.1.1k - OpenSSL
Changes between 1.1.1l and 1.1.1m [xx XXX xxxx] *) Changes between 1.1.1k and ... [Richard Levitte] *) Have 'config' recognise 64-bit mingw and choose ... https://www.openssl.org |
|
